Strengthen Your Defenses with Data Cyber Security Solutions for Better Protection
Strengthen Your Defenses with Data Cyber Security Solutions for Better Protection
Blog Article
How Information and Network Safety Secures Versus Arising Cyber Dangers
In an era marked by the fast development of cyber threats, the relevance of information and network safety has actually never ever been a lot more pronounced. As these hazards end up being a lot more complicated, comprehending the interaction between data safety and security and network defenses is important for alleviating risks.
Recognizing Cyber Hazards

The ever-evolving nature of technology continuously presents brand-new susceptabilities, making it necessary for stakeholders to continue to be vigilant. Individuals may unconsciously fall victim to social engineering tactics, where aggressors adjust them right into revealing sensitive details. Organizations face special challenges, as cybercriminals often target them to make use of beneficial data or disrupt operations.
Additionally, the surge of the Internet of Things (IoT) has increased the attack surface, as interconnected tools can serve as access points for assaulters. Acknowledging the importance of robust cybersecurity methods is crucial for minimizing these risks. By cultivating an extensive understanding of cyber individuals, threats and companies can execute effective techniques to secure their digital possessions, making sure resilience in the face of an increasingly complex threat landscape.
Trick Components of Information Security
Making certain data safety needs a multifaceted method that includes different key parts. One basic element is information encryption, which changes delicate info right into an unreadable layout, available just to authorized customers with the proper decryption tricks. This functions as a critical line of defense versus unauthorized access.
One more vital part is accessibility control, which controls that can check out or control information. By carrying out strict customer verification methods and role-based access controls, companies can decrease the risk of expert risks and information violations.
Furthermore, information masking strategies can be used to safeguard delicate information while still enabling its usage in non-production settings, such as testing and growth. fft perimeter intrusion solutions.
Network Safety And Security Strategies
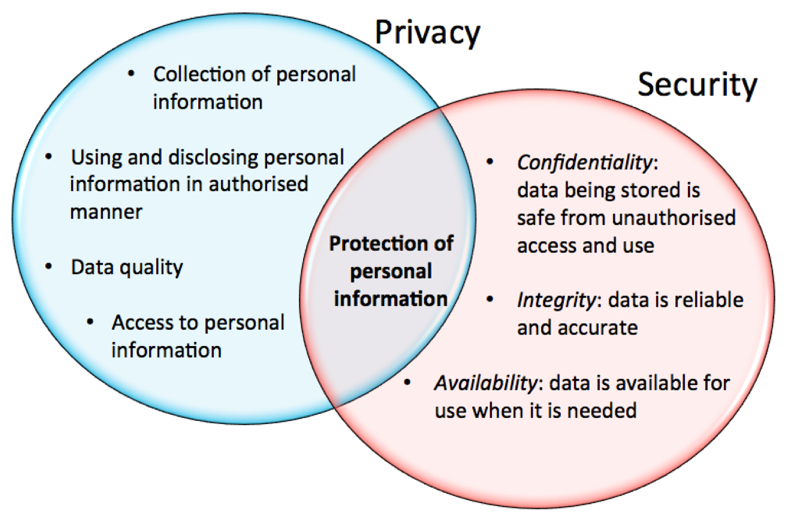
Implementing robust network safety and security approaches is vital for protecting an organization's electronic framework. These methods entail a multi-layered method that includes both equipment and software remedies made to protect the stability, privacy, and schedule of data.
One important element of network safety is the release of firewalls, which function as an obstacle in between trusted inner networks and untrusted outside networks. Firewalls can be hardware-based, software-based, or a combination of both, and they assist filter outbound and incoming website traffic based on predefined safety and security policies.
Additionally, intrusion discovery and avoidance systems (IDPS) play an important duty in keeping an eye on network website traffic for questionable activities. These systems can inform managers to potential breaches and act to reduce risks in real-time. Regularly patching and upgrading software is also important, as vulnerabilities can be exploited by cybercriminals.
Additionally, executing Virtual Private Networks (VPNs) ensures safe remote gain access to, securing information sent over public networks. Segmenting networks can lower the strike surface area and contain possible breaches, limiting their influence on the total infrastructure. click over here By embracing these approaches, organizations can efficiently fortify their networks versus arising cyber risks.
Ideal Practices for Organizations
Establishing finest methods for companies is vital in keeping a solid safety pose. A comprehensive method to data and network security begins with regular risk analyses to recognize vulnerabilities and possible risks.
Additionally, continuous employee training and understanding programs are essential. Staff members must be informed on identifying phishing efforts, social design techniques, and the importance of sticking to safety and security procedures. Regular updates and patch management for software application and systems are also important to protect against understood susceptabilities.
Organizations must develop and examine case response intends to make certain preparedness for potential breaches. This consists of developing clear communication networks and roles during a protection case. In addition, information security must be utilized both at rest and en route to guard delicate info.
Finally, performing periodic audits and compliance checks will certainly aid ensure adherence to well-known policies and relevant laws - fft perimeter intrusion solutions. By adhering to these ideal practices, organizations can considerably improve their resilience against arising cyber dangers and secure their important assets
Future Trends in Cybersecurity
As organizations browse a progressively intricate electronic landscape, the future of cybersecurity is positioned to evolve significantly, driven by shifting and arising innovations danger standards. One popular trend is the combination of fabricated intelligence (AI) and artificial intelligence (ML) into security structures, permitting real-time danger detection and reaction automation. These innovations can assess substantial amounts of information to determine anomalies and potential violations much more efficiently than conventional approaches.
Another critical pattern is the rise of zero-trust architecture, which calls for constant verification of user identities and device safety, no matter of their area. This approach minimizes the threat of expert risks and enhances defense versus external you can try this out assaults.
Additionally, the enhancing adoption of cloud services demands durable cloud safety and security strategies that resolve distinct vulnerabilities connected with cloud settings. As remote work becomes an irreversible component, securing endpoints will also come to be paramount, causing a raised concentrate on endpoint detection and reaction (EDR) remedies.
Last but not least, regulatory compliance will remain to shape cybersecurity methods, pressing organizations to embrace more stringent data defense actions. Embracing these trends will certainly be important for companies to fortify their defenses and navigate the developing landscape of cyber threats successfully.
Verdict
In verdict, the implementation of robust data and network protection measures is essential for companies to guard against emerging cyber threats. By making use of encryption, access control, More Bonuses and reliable network protection techniques, companies can considerably decrease susceptabilities and safeguard delicate details.
In a period marked by the quick advancement of cyber threats, the importance of information and network safety has never ever been much more noticable. As these dangers become a lot more complicated, understanding the interplay between data safety and security and network defenses is crucial for minimizing risks. Cyber risks include a large range of harmful activities intended at endangering the discretion, honesty, and accessibility of networks and information. A thorough method to data and network safety starts with routine danger evaluations to identify vulnerabilities and potential dangers.In conclusion, the implementation of durable data and network safety and security actions is crucial for organizations to secure against arising cyber risks.
Report this page